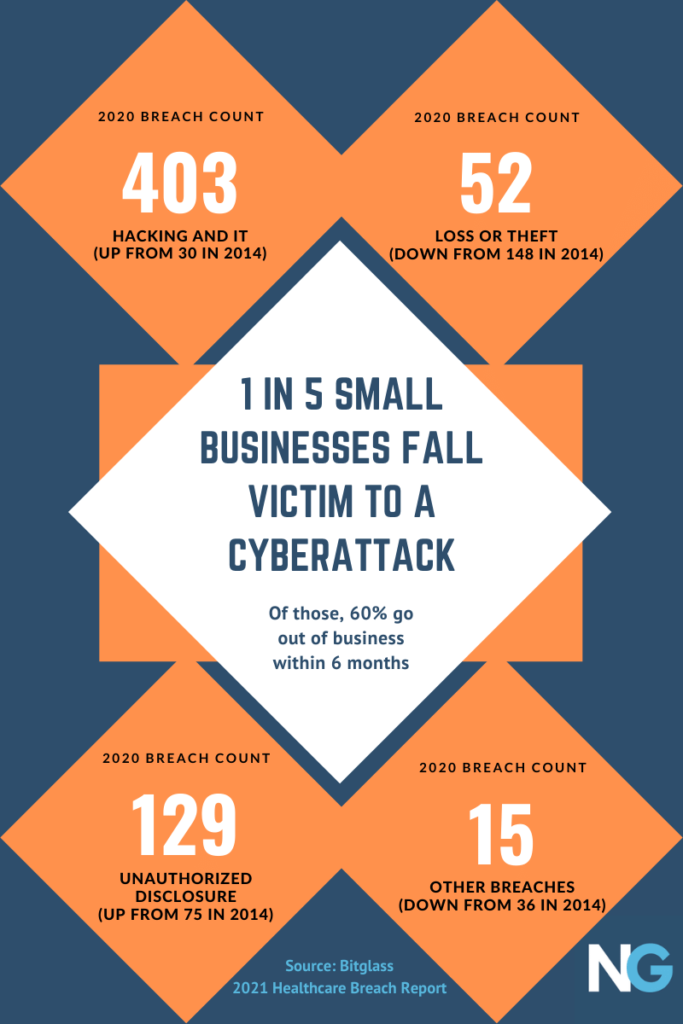
Data breaches continue to become more and more common. In 2021, the Identity Theft Research Center reported a record number of data breaches, amounting to a 68% increase over the previous year. That same year, the average cost of a data breach was $4.24 million dollars.
Business leaders know the threat is increasing. But, only 5% of companies’ folders are properly protected.
Let’s take the China leak, for example. In July of 2022, a hacker claimed they‘d breached the Shanghai police department database. They later attempted to sell over 23 terabytes of data on almost 1 billion Chinese citizens for 10 Bitcoin, or $236,542 at the time of this writing.
Here’s what the hacker supposedly gained access to:
- Names and birthplaces
- National ID numbers
- Phone numbers
- Medical records
- Police reports
This proves that no one is safe. So, what should you do in the event of a data breach? Read on to find out.
Types of business data breaches
Some of the most common types of data breaches include malicious attacks, destructive/ ransomware attacks, and nation-state attacks.
Malicious attacks can occur due to a variety of factors including gaps in the cloud, system glitches, or vulnerabilities in third-party software. These attacks may also involve stolen or leaked information that a hacker might have obtained through the black market.
Destructive and ransomware attacks are some of the most dangerous forms of data breaches. They occur when someone destroys records or takes sensitive information in an attempt to hold it for ransom.
Nation-state attacks can be the most costly type of data breach, even though they don’t happen as often as malicious or ransomware attacks. They occur when hackers partner with government officials to commit crimes against the U.S. and/or any of its allies.
What should businesses do after a data breach?
If your business is a victim of a data breach, you need to take certain steps right away–to protect yourself, your company, and your customers. Here is what you can do:
1. Confirm the breach
You should have a dedicated team assembled ahead of time, tasked with handling emergency situations like data breaches. You may have an Intrusion Prevention System (IPS), but that alone is not enough. You still need to have your own team if these circumstances arise. Before you take any further action, confirm with your security team that a data breach actually occurred.
After confirming the breach, closely monitor every entry and exit point while paying close attention to the ones involved in the breach.
2. Identify the source and extent of the breach
After confirming a breach, your next steps will depend on the severity of the data leak. After confirming that a breach happened, your next step is to assess the situation.
First you’ll need to interview the person who discovered it and ask them how they came to that conclusion and what happened prior to their discovery. Your investigation should lead you directly to the source. If you have intrusion detection and prevention software, even better—these systems will make it easy to identify the source. If not, however, finding the true source of the breach will be an added challenge.
When investigating, it is important to document your findings. Experts recommend that you save a copy of all affected servers for legal purposes.
3. Fix vulnerabilities
After the investigation into what caused the data breach, you should have a clear understanding of how to fix it and prevent it from happening again.
If any third-party service providers were involved, examine the personal information they have access to and decide if you need to change or modify access privileges. All of your service providers should be taking steps to prevent another data breach, but it’s up to you to confirm these measures are being taken. If they tell you that vulnerabilities have been removed, ensure it was done. Then, request that additional measures, like encryption features, be added.
Test to Make Sure your Cybersecurity Defenses Work
After a data breach, make sure all the cybersecurity practices and procedures you put in place are effective. Test all servers and virtual machines because these devices tend to be the most vulnerable. Implement new security measures if necessary. Once you have established this, replace all affected machines with clean machines. Update credentials and passwords for authorized users if necessary.
4. Notify appropriate parties
Begin by notifying the law. Contact your local police department and data protection authorities to report the situation.
If you hold information on behalf of other businesses, contact those companies to alert them. If account access info like credit card or bank account numbers were stolen but you are not responsible for maintaining those accounts, contact the institution that does. When notifying individuals of a data breach, companies are encouraged to have someone from their organization responsible for communicating the information with those who have been affected. This is extensive, but important because many people may want to freeze their credit reports to prevent identity theft. If the compromise involved a large group of individuals, advise the credit bureaus.
You should be proactive and take steps to ensure that you do not experience additional data breaches. You should disconnect all affected equipment from your network immediately, but do not shut down any machines until forensic experts arrive.
5. Prevent future breaches
After you have pinpointed the source of the data breach, you should have instilled procedures to prevent it from happening again. You can prevent recurrences by creating a formal contingency plan for future cases and tracking what happened in some kind of project management software. Despite a data breach being resolved, the incident can still have severe impacts. Proactive measures can reduce the chance of reoccurrence.
After a data breach, continue communicating with customers. Let them know what happened, how the situation was resolved, and what security measures have been implemented. Explain in detail what led to the breach and accept responsibility for any fault on your part. Accepting responsibility shows integrity and builds trust with customers.
Have your IT security team continue to evaluate the threat on behalf of your business, so it doesn’t happen again.
Here are some tips to prevent a data breach in the future:
Train your employees
Sometimes, data breaches aren’t because of a hacker who purchased your information from the dark web. It could have been the fault of an employee. In fact, 88% of data breaches are caused by human error.
Train your people to follow best practices such as using strong passwords, and make sure they know never to give their credentials away. They should be educated on all common cybersecurity threats so that they know what to look out for and what to avoid. Then establish and set up protocols. Make sure everyone knows the steps to take in the event of a data breach and who’s responsible for what.
Restrict access
Limiting user access reduces the number of potential vulnerabilities in a system. For example, if 100 people log in to your system daily and it houses personal information, there are 100 potential vulnerabilities. Limiting access to only a restricted few reduces this number greatly because this means you are only allowing access to those who need to use the system.
To prevent unauthorized access, do not store certain kinds of data, such as credit card numbers. Assign user roles with different levels of access to all your internal systems.
Improve general security
There are lots of ways to keep your data protected, but the best way is by adding more layers, like firewalls and VPNs. These additional measures are easy to set up and can keep your information from getting into the wrong hands. Evaluate all third-party vendors carefully. Never connect with any unsecured organization.
A CASB (cloud access security broker) is the modern way to keep your information safe in the cloud. CASBs give you continuous visibility, data protection and monitoring for all files stored on remotely accessed storage solutions such as Dropbox or Google Drive that use SSL encryption protocols.
In addition, these brokers offer machine learning tools so an organization can identify any unauthorized users before it’s too late; when hackers try accessing sensitive documents without permission—an alarm goes off immediately.
The system’s security measures will automatically block access attempts if someone tries to use the computer while it is unattended. No one will be able to access the system unless given explicit approval by managers first.
In a networked world, businesses must use cutting-edge technologies to secure their information. CASBs help manage cloud services by auditing them for vulnerabilities and blocking risky services from being used, while providing data protection with encryption and tokenization for sensitive information stored online.
Businesses that have not experienced data breaches may think that they are unlikely to occur. Instead, it’s essential to have a completely different mindset as a data breach is not a matter of if but when.
To prevent data breaches, stay vigilant and take active measures to secure your company’s information. If a breach does occur, immediately identify the source and extent of the breach, fix vulnerabilities, and notify all affected parties.
Frequently asked questions
What is a data breach?
A data breach is unauthorized access, use, or disclosure of personal or confidential information. This can include personally identifiable information (PII) and sensitive business information. Data breaches can be unintentional or malicious.
Data breaches can occur when an organization fails to protect its users’ data from hackers, employees who are not authorized to access specific data or a malicious attack on the company’s computer systems.
What are examples of data breaches?
Data breaches are a serious issue for businesses, but it can be hard to tell when one happens. Here are some common examples of data breaches:
Hacking: Hackers gain access to sensitive information by bypassing security systems or exploiting existing vulnerabilities.
Lost or stolen devices: When an employee loses their laptop or smartphone or gets stolen, that device may contain sensitive business information.
Unsecured cloud storage: If your company uses cloud-based storage and you don’t properly secure your data, hackers could compromise it.
Manipulation of data: If you have access to sensitive information, you might be able to change it or delete it before anybody notices.
What happens when data is breached?
When data is breached, it can have a number of different effects on your business. The first thing that happens is that your company is put at risk for financial loss and reputation damage. You may face lawsuits from customers who are affected by the breach, or you could lose new customers who choose not to do business with you because they don’t want to be part of a company that has been breached in the past.
Customers may distrust your brand and choose not to do business with you because they fear their personal information could be compromised again in the future. People may question your lapse in security.
There could also be legal consequences for failing to protect personal data.
Author bio: Irina Maltseva is a Growth Lead at Aura and a Founder at ONSAAS. She’s been helping SaaS companies grow their revenue for the last seven years. At Hunter, Irina helped 3M marketers build business connections that matter. Now at Aura, Irina is working on her mission to create a safer internet for everyone. To get in touch with Irina, follow her on LinkedIn.
Disclaimer: This article is for general informational purposes only and should not be taken as legal or professional advice. The views and opinions expressed in this article are solely those of the author and do not necessarily reflect the views of our organization. We do not endorse any products or services mentioned in the article.